Why All The Emphasis On Insider Threats? Three Reasons:
 1. Insider security risks are more prevalent and potentially more damaging.
1. Insider security risks are more prevalent and potentially more damaging.
According to a study conducted by the Ponemon Institute, 34% of data breaches in the U.K., come from malicious activity, including criminal insiders, and 37% of breaches come from employee negligence. A previous Ponemon study indicated that a third of malicious attacks come from criminal insiders. Further, a Forrester study revealed that 75% of data breaches were caused by insiders, most often due to employee negligence or failure to follow policies. The most-often cited incidents were lost devices, inadvertent misuse of sensitive information and intentional theft of data by employees. The impact of data breaches and downtime, whether caused by insider malice or negligence, can cripple an organization, exposing it to lost revenue, significant brand damage and increasingly onerous regulatory fines and penalties.
2. User identity “blind spots” are causing audit failures.
Many organizations are failing audits because of blind spots in their identity infrastructures. Blind spots can occur when identities and entitlements are managed in disparate silos or on local servers rather than centrally. For example, one of the biggest identity challenges for companies — and a major cause of failed audits — is a lack of visibility into local administrator accounts on Windows. This is akin to the root account on a Linux/Unix system. Failed audits can be particularly damaging in today’s environment, in which regulations related to data loss and data protection are becoming more rigorous around the world. Companies that conduct business globally have to be in compliance with a wide range of rules and regulations to satisfy audit requirements.
As such, organizations must be able to provide proof that users who have access to certain servers and applications are actually authorised users. They must also be able to deliver an auditable trail of what each user has done within the server. These requirements mean organizational policies need to apply the principle of “least privilege access,” whereby users log in as themselves and have only those privileges needed to do their jobs. If they need to have their privilege elevated for some reason, that is an explicit action.
3. Organizational complexity is posing a growing challenge.
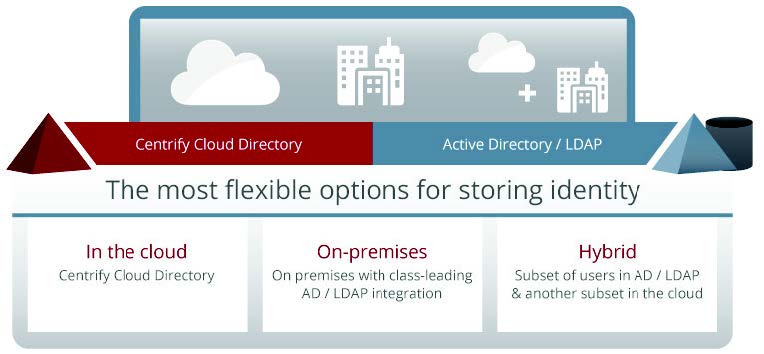
Managing employee identity used to be relatively easy: A user was typically sitting at a desktop with a single machine connected to an enterprise application through a single wire. Ah, but things have changed. Users are now mobile and using a wide range of devices, some of which may be unsanctioned or undocumented personal devices. And mobility is only one aspect of the heightened complexity. IT infrastructures are increasingly diverse and heterogeneous, with multiple silos defined by departments, applications, operating systems or other characteristics that set them apart from one another. The proliferation of virtualization and cloud services adds additional layers of complexity to the IT environment. Without a solution to unify user identities, organizations face the prospect of having too many identities, thus raising too many identity-related risks — including data loss, data breaches, application downtime, failed audits and an inability to identify and rectify internal security problems before they escalate.
Savvy IT and security managers are recognizing that the most cost-efficient and effective way to address these challenges is to incorporate a solution that provides insiders with a unified identity across all platforms. By linking access privileges and activities to specific individuals, the IT organization can establish the control needed to minimize security risks, along with the visibility required to achieve compliance.
© 2013 Centrify Top 3 Reasons to Give Insiders a Unified Identity.
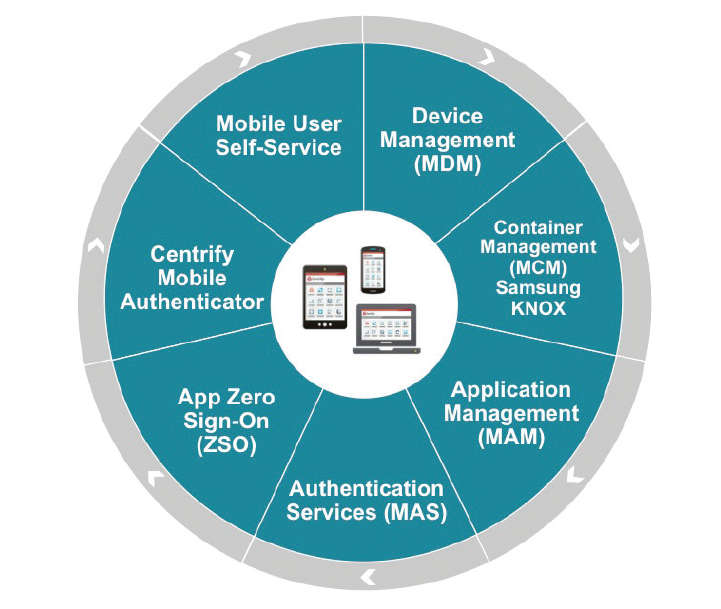
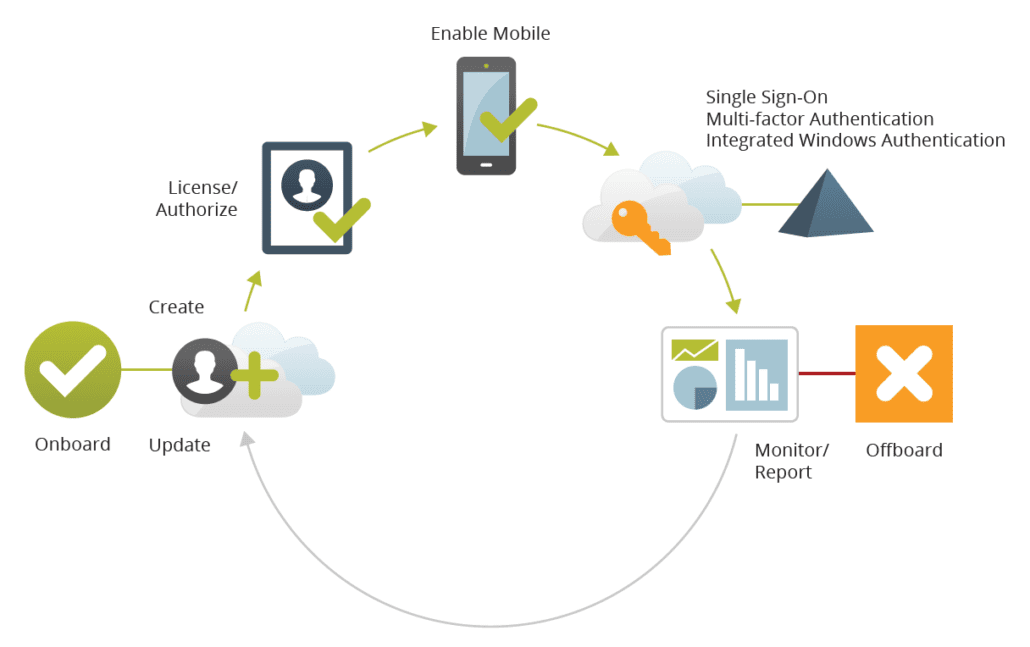
Centrify is a PathMaker Group partner providing advanced privileged access management, enterprise mobility management, cloud-based access controls worldwide. The Centrify Identity Service provides a SaaS product that includes SSO, multi-factor authentication, enterprise mobility management and seamless application integration. The Centrify Privilege Service provides simple cloud-based control of all privileged accounts and provides extremely detailed session monitoring, logging and reporting capabilities. The Centrify Server Suite provides the ability to leverage Active Directory as the source of privilege and access management across your Unix, Linux and Windows server infrastructure. Centrify is a Leader in The Forrester Wave, Q3 2016.

 1. Insider security risks are more prevalent and potentially more damaging.
1. Insider security risks are more prevalent and potentially more damaging.