20/20 Vision: Identity and Access For The Next Decade
As attacks become more difficult to detect and defend, and threats
continue to grow, no organization is immune from security breaches.
We anticipate a shift around identity and access management (IAM) as
enterprises cope with increased regulatory compliance requirements,
insider and external threats, cloud integration, and more.
IBM Security threat aware IAM solutions help prepare you for current and
future security challenges with identity intelligence and secure online
access in mobile, cloud, mainframe, and social environments.
Explore IBM Security identity and access management
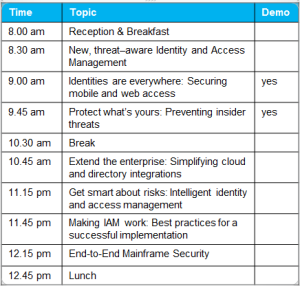
Join IBM and Pathmaker Group and learn how to:
• Use security intelligence to improve user oversight and compliance.
• Respond effectively to the rising number of identity focused attacks.
• Safeguard access within mobile, cloud, mainframe and social
environments.
• Protect against advanced insider threats.
Don’t miss this chance to network with your peers, talk to IBM security
experts, and get practical advice for your own IAM environment.